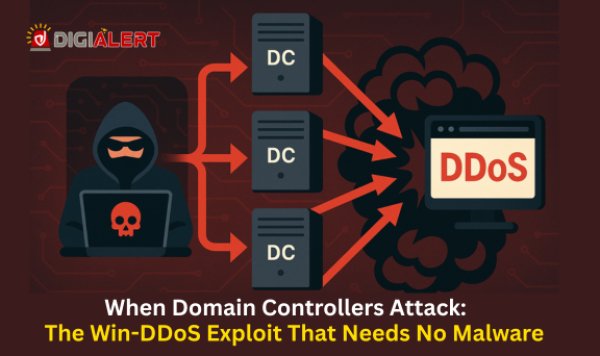
Did you know that a single vulnerable Windows system can be weaponized to launch devastating DDoS attacks?
Recent cybersecurity discoveries have revealed critical flaws in Windows systems that could be exploited to orchestrate massive Distributed Denial-of-Service (DDoS) attacks. In 2024 alone, the number of DDoS incidents surged by an alarming 74%, making this one of the most pressing threats for organizations worldwide.
As cybercriminals refine their tactics, these vulnerabilities are turning everyday systems into powerful attack tools—without their owners even realizing it. At DigiAlert, our cybersecurity experts are dissecting this threat, explaining its impact, and offering clear strategies to keep your organization safe.
Understanding the New Windows DDoS Vulnerabilities
The latest findings indicate that certain flaws in Windows network handling and protocol execution can be exploited remotely. Once compromised, a Windows system can be hijacked and integrated into a botnet—a network of infected devices used to execute coordinated cyberattacks.
Why this is dangerous:
- Amplification Power: A single infected machine can produce traffic volumes of up to 2.3 terabits per second (Tbps)—enough to overwhelm even enterprise-grade defense systems.
- Stealth Factor: Many infected systems continue functioning normally, making detection difficult until significant damage is done.
- Global Reach: Attackers can use compromised systems from different countries, making mitigation and attribution challenging.
This is not just a theoretical risk—it’s a clear and present danger affecting businesses across industries, especially financial services, healthcare, and e-commerce, where service downtime can result in millions in losses.
The Scale of the DDoS Threat in 2025
DDoS attacks are not new, but their sophistication and impact have grown exponentially. According to Netscout’s 2024 Threat Intelligence Report, attackers launched over 15 million DDoS attacks worldwide last year, with the average attack bandwidth increasing by 40%.
Key statistics:
- 74% increase in total DDoS incidents year-on-year.
- 45% of large-scale attacks now exceed 1 Tbps.
- 60% of attacks last more than 30 minutes, giving hackers more time to achieve their objectives.
- The average cost of a DDoS attack for a mid-sized company: $218,000 per incident, factoring in downtime, remediation, and lost revenue.
When we look at the Windows-specific vulnerabilities uncovered this year, it’s clear that these flaws significantly lower the barrier for attackers to generate large-scale, disruptive attacks.
Industries Most at Risk
1. Financial Services
Banks, trading platforms, and fintech providers depend on uninterrupted service. Even a brief outage can result in halted transactions, regulatory scrutiny, and reputational damage.
2. Healthcare
Hospitals and telemedicine platforms rely on real-time data access for patient care. A DDoS-induced outage could disrupt life-saving operations.
3. E-commerce & Retail
Online marketplaces depend heavily on uptime, especially during sales periods. Downtime means lost sales, abandoned carts, and dissatisfied customers.
4. Government & Critical Infrastructure
Disruption to public service portals or municipal systems can have wide-ranging social and economic consequences.
How Attackers Exploit These Flaws
The newly disclosed vulnerabilities allow attackers to send crafted network requests to Windows systems, triggering resource-intensive processes that can crash or slow down devices. Once infected, the systems are enrolled in a DDoS-for-hire service—where cybercriminals rent out access to botnets for a fee.
For example:
- A hacker could use 10,000 compromised Windows PCs to flood a corporate network with malicious traffic.
- With an average capacity of 2.3 Tbps per device, the combined impact can exceed 23 petabits per second, which is enough to take down large-scale cloud infrastructure.
Why Traditional Security Measures Aren’t Enough
While basic antivirus and firewalls are important, they are not equipped to handle the scale and speed of modern DDoS attacks. Many organizations discover an infection only after their systems are already being used in an attack—by then, damage to reputation and operations has already occurred.
Common gaps include:
- Infrequent Patching: Many companies delay updates due to compatibility concerns, leaving exploitable gaps.
- Lack of Network Visibility: Without continuous traffic monitoring, abnormal patterns go unnoticed.
- Overreliance on Perimeter Defenses: Firewalls can block some attacks, but distributed botnets bypass these protections.
DigiAlert’s Recommended Defense Strategy
At DigiAlert, we advocate for a multi-layered approach to cybersecurity that includes:
1. Immediate Patch Management
Ensure all Windows systems are updated with the latest security patches. Vulnerabilities often get publicly documented, meaning attackers move quickly to exploit them.
2. Advanced Traffic Monitoring
Deploy tools capable of real-time traffic inspection. Anomalies—like unusual outbound traffic or sudden spikes—should trigger automated alerts.
3. Zero-Trust Network Architecture
Implement a zero-trust model, which treats every device and user as unverified until proven otherwise. This limits the movement of attackers inside your network.
4. DDoS Mitigation Services
Consider integrating cloud-based DDoS protection that can absorb and filter attack traffic before it reaches your servers.
5. Incident Response Planning
A rapid response plan ensures your team knows exactly what to do in the event of a breach or attack, reducing downtime and loss.
Case Study: Real-World Impact of a Windows DDoS Exploit
In late 2024, a European e-commerce platform experienced a 1.8 Tbps DDoS attack traced back to compromised Windows machines. The attack lasted for 90 minutes, causing:
- Loss of $1.2 million in sales during a peak shopping event.
- Reputational harm as customers shared outage complaints on social media.
- Emergency IT costs of over $80,000 for recovery and mitigation.
Post-incident analysis revealed the vulnerability had been patched by Microsoft months earlier—but the organization had delayed updates, exposing themselves to avoidable risk.
The Road Ahead for Organizations
Cybercriminals are not slowing down. As long as vulnerabilities exist, they will be exploited. Businesses must shift from a reactive to a proactive cybersecurity posture.
What proactive defense looks like:
- Continuous Vulnerability Scanning: Detect weaknesses before attackers do.
- Employee Security Training: Educate teams about phishing, suspicious emails, and malware risks.
- Collaboration with Threat Intelligence Providers: Partner with firms like DigiAlert to gain early warning on emerging threats.
Final Thoughts
The latest Windows DDoS vulnerabilities are a stark reminder that cyber threats are evolving faster than many organizations’ defenses. Ignoring patch management, relying solely on perimeter defenses, or assuming “we’re not a target” are dangerous mindsets.
By combining immediate patching, continuous monitoring, and zero-trust frameworks, businesses can dramatically reduce the risk of being caught in the next massive botnet-powered attack.
- Follow DigiAlert for continuous updates on the latest cybersecurity threats and defense strategies.
- Follow VinodSenthil for expert insights into protecting your digital infrastructure from emerging risks.