- Python
- JavaScript
- Go
- C++
- Bash
- Rust
- Ruby
- C
- TypeScript
- OCaml
- PHP
- Java
- C#
Introducing codeALERT - Your AI-Based SAST Source Code Auditing Solution
At digiALERT, we are delighted to present codeALERT, our cutting-edge Static Application Security Testing (SAST) product. Developed using advanced artificial intelligence (AI) techniques, codeALERT is specifically designed to provide organizations with comprehensive source code auditing capabilities. With codeALERT, you can identify and address potential vulnerabilities in your codebase, fortifying your applications against cyber threats and enhancing your overall security posture.

SAST Product
SAST stands for Static Application Security Testing. A SAST product is a type of security tool used in software development to analyze the source code or compiled code of an application for security vulnerabilities and weaknesses. SAST tools perform a static analysis of the code without executing the application, searching for potential vulnerabilities such as coding errors, insecure coding practices, or known security issues.
SAST products use various techniques, including pattern matching, data flow analysis, and control flow analysis, to identify security vulnerabilities in the code. They can detect issues such as SQL injection, cross-site scripting (XSS), buffer overflows, and insecure data handling.
The primary goal of a SAST product is to identify security vulnerabilities early in the development process, allowing developers to fix them before the application is deployed. By integrating SAST tools into the development workflow, organizations can proactively address security issues and reduce the risk of potential exploits and breaches.
- SAST products use various techniques, including pattern matching, data flow analysis, and control flow analysis, to identify security vulnerabilities in the code. They can detect issues such as SQL injection, cross-site scripting (XSS), buffer overflows, and insecure data handling.
The primary goal of a SAST product is to identify security vulnerabilities early in the development process, allowing developers to fix them before the application is deployed. By integrating SAST tools into the development workflow, organizations can proactively address security issues and reduce the risk of potential exploits and breaches.
Automated AI/ML based scanner
Automated AI/ML-based scanners offer several benefits in the field of cybersecurity and vulnerability management. Here are some key


Supporting languages

Python

JavaScript
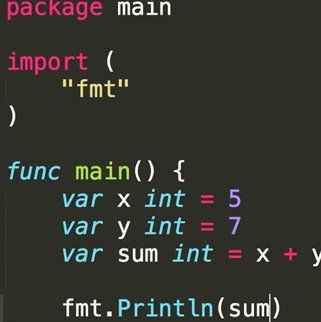
Go

C++

Bash

Rust
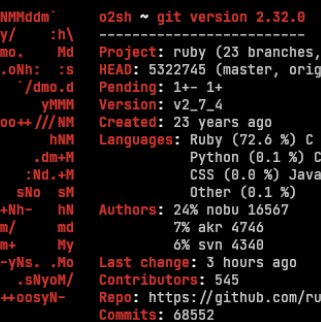
Ruby

C

TypeScript

OCaml

PHP

Java

C#
(saas/onprem)
Operational Models
Software as a Service (SaaS)
On-Premises (On-Prem)
Comparison

Experience the Power of codeALERT for Source Code Auditing
OWASP Top 10
The OWASP (Open Web Application Security Project) Top 10 is a widely recognized and respected list of the most critical security risks facing web applications. When it comes to source code auditing and review, following the OWASP Top 10 guidelines is crucial to identify and mitigate potential vulnerabilities.
- With codeALERT, you can proactively identify and mitigate vulnerabilities in your source code, strengthening the security of your applications. By leveraging the capabilities of AI, codeALERT empowers your development team to build robust and secure software while adhering to industry best practices. Take the next step in enhancing your source code security by contacting us today. Our team will be delighted to provide you with more information on how codeALERT can safeguard your applications against potential threats.
Injection Attacks
Auditing source code should focus on preventing SQL, OS, and other injection attacks by validating and sanitizing user input, using parameterized queries, and avoiding concatenation of user input with queries or commands.
Broken Authentication and Session Management
Cross-Site Scripting (XSS)
Insecure Direct Object References
Security Misconfigurations
Sensitive Data Exposure
XML External Entities (XXE)
Broken Access Control
Security Logging and Monitoring
Insufficient Security Testing






