Table Of Contents
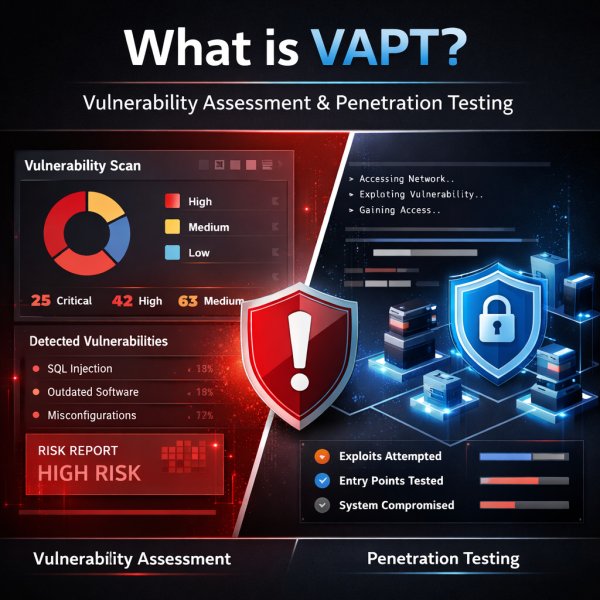
What Is VAPT?
VAPT is made up of two parts:
Vulnerability Assessment is Finding known security flaws in your systems, apps, devices, or network is called a vulnerability assessment. Issues like outdated software, unsafe setups, missing patches, insufficient encryption, exposed services, and known CVEs are often scanned, analysed, and prioritized.
Penetration testing goes a step further. It simulates real-world attack behavior to determine whether those weaknesses can actually be exploited, how far an attacker could go, and what business impact that exploitation could cause. NIST defines penetration testing as testing that verifies how well a system resists active attempts to compromise its security.
Why You Need Both
Each approach has blind spots when used alone. A vulnerability scan indicates potential vulnerabilities but not their true severity. Pen testing reveals the complete extent of an attacker's potential, but only if they are aware of where to concentrate.
When combined, VAPT provides you with the whole picture, including a comprehensive list of vulnerabilities and a practical comprehension of their implications for your company.
Why VAPT Matters More Than Ever
Modern businesses are exposed from multiple directions at once. You are not just protecting one office network anymore. You are protecting:
- web applications
- mobile apps
- APIs
- cloud workloads
- employee endpointsthird-party integrations
- remote access systems
- SaaS platforms
- customer data
- internal admin portals
Every one of those creates attack surface.
IF your business is connected to the internet, your business is a target
What Does VAPT Actually Check?
A proper VAPT exercise can cover several layers depending on scope. Common areas include:
Web Application Security
This includes testing login flows, session handling, broken access control, input validation, authentication logic, business logic flaws, file upload issues, insecure admin functions, and common attack vectors such as SQL injection, XSS, and CSRF. OWASP’s Web Security Testing Guide is one of the main reference points for this kind of testing.
Mobile Application Security
Android and iOS apps can expose hardcoded secrets, insecure local storage, weak API protections, poor session control, and broken authorization.
API Security Testing
Many companies now rely heavily on APIs, but APIs are often under-tested. Weak authentication, excessive data exposure, broken object-level authorization, and poor rate limiting are common failure points.
Network Security Testing
This covers exposed ports, insecure services, firewall gaps, VPN weaknesses, weak segmentation, and internal lateral movement risks.
Cloud Security Testing
Cloud environments often fail due to misconfiguration rather than advanced hacking. Public buckets, over-permissive IAM roles, unmanaged keys, open management interfaces, and insecure security group rules are common problems.
Internal Security Testing
This simulates what happens if an attacker gets inside your environment through phishing, a compromised laptop, or a stolen VPN credential.
Why Your Business Needs VAPT Right Now
Let's be direct: cybersecurity threats are not slowing down. Ransomware attacks, data breaches, phishing campaigns, SQL injections these aren't hypothetical scenarios. They're happening to businesses of all sizes every single day.
Here's why VAPT specifically deserves a place in your security strategy:
1. Cybercriminals Are Getting Smarter
Attackers nowadays do not use brute force to get past firewalls. They search for even the smallest vulnerabilities, such as an unpatched software version, a wrongly configured cloud storage bucket, or a vulnerable API endpoint. These fissures are discovered first by VAPT.
2. Regulatory Compliance Is Non-Negotiable
If your business handles personal data, payment information, or health records, you likely fall under regulations like GDPR, PCI DSS, HIPAA, ISO 27001, or India's DPDP Act. Many of these frameworks explicitly require regular security testing. VAPT helps you meet compliance requirements and avoid costly fines.
3. A Data Breach Is Expensive. VAPT Is Not.
The average cost of a data breach globally is now over $4.4 million according to IBM's Cost of a Data Breach Report. VAPT, by comparison, is a fraction of that cost and it gives you the chance to fix vulnerabilities before they become breaches. The ROI here is straightforward.
4.Remote Work Has Expanded Your Attack Surface
Hybrid workforces, BYOD policies, cloud migrations, third-party integrations all of these have made the modern IT environment dramatically more complex and harder to secure. VAPT maps your entire attack surface, including the parts your internal team might not even know about.
5.Trust Is Your Most Valuable Asset
Customers, partners, and investors want to know that their data is safe with you. Being able to demonstrate regular, independent security testing isn't just good practice it's a competitive differentiator. In a world where one breach can destroy years of brand reputation, VAPT is part of protecting what matters most.
Who Should Get VAPT Done?
In a nutshell: nearly all businesses that rely on digital infrastructure.
Nevertheless, VAPT is particularly important for:
• Financial organizations, including banks, NBFCs, and fintech firms
• Healthcare providers, including clinics, hospitals, and health technology
• E-commerce companies anyone who keeps client or payment information
• SaaS firms: cloud-based systems that manage user information
• Public sector and governmental entities
• As startups raise capital, investors are requesting more security posture evidence.
• Enterprises with remote or distributed teams
If your business stores any form of sensitive data, accepts online payments, or relies on a web application or API to deliver services - you need VAPT.
How Often Should a Business Do VAPT?
There is no universal frequency that fits every business, but these are sensible triggers:
- before launching a new application
- after major code changes
- after infrastructure or cloud migration
- before enterprise onboarding or audits
- after integrating third-party systems
- after significant security incidents
- at least annually for baseline assurance
- more frequently for internet-facing or high-risk systems
If your application changes every month and you do VAPT once a year, your testing cadence is disconnected from your actual risk.
FAQ About VAPT
1. Does VAPT help with compliance?
Yes. VAPT is often required or expected as part of broader security and compliance programs, though compliance alone should not be the only reason to do it.
2. Is VAPT only for large enterprises?
No. That assumption is outdated. Small and mid-sized businesses are often easier targets because they usually have fewer dedicated security controls, weaker monitoring, and faster but less-governed development cycles. If your business has a website, cloud setup, mobile app, API, remote users, or customer data, VAPT is relevant.
3. Can VAPT be done without affecting business operations?
Yes, if it is planned properly. A professional VAPT engagement is usually scheduled with clear rules of engagement, test windows, excluded systems if required, and rollback/escalation contacts. Guidance around security testing emphasizes planning and controlled execution to reduce business disruption.
4. Is automated scanning enough for security testing?
No. Automated scanning is useful for breadth, but it does not replace manual validation, attack chaining, business logic testing, or proof of exploitability. OWASP’s testing guidance makes that point very clearly.
5.Will VAPT help identify misconfigurations in cloud environments?
Yes. It can identify issues like public storage, weak IAM, exposed services, and insecure cloud settings.
Final Thoughts
VAPT is not just a technical exercise. It is a business protection mechanism.It helps you identify weak points before they turn into incidents. It gives leadership visibility into real risk. It improves security maturity. It supports compliance. It strengthens customer confidence. Most importantly, it reduces the chance that your organization becomes the next easy target.
The smart move is simple: Test early, Test properly, fix fast, and retest.
Call to Action
If your business has a website, mobile app, API, cloud workload, or exposed infrastructure, now is the right time to assess your security posture.
Get in touch with digiALERT for a structured security review, actionable findingsand remediation guidance that actually helps you reduce risk.
Schedule Your VAPT Scoping Call with digiALERT today - BOOK NOW