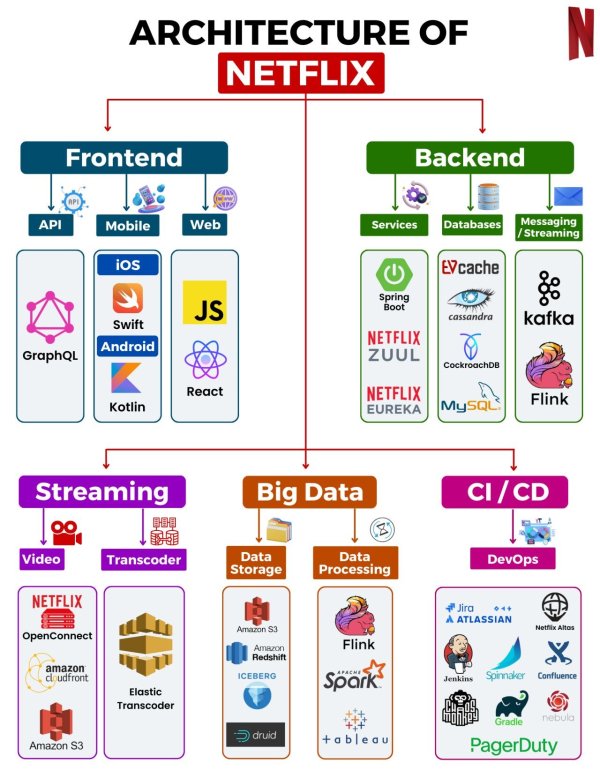
As cybersecurity professionals, our mission is to thoroughly analyze the architecture of Netflix and identify potential security vulnerabilities. While this analysis is based on hypothetical assumptions, it provides valuable insights into the potential threats that a large-scale organization like Netflix may encounter. In this comprehensive blog post, we will examine each component of the Netflix architecture, outlining potential attack vectors and emphasizing the importance of implementing robust security measures.
Frontend: GraphQL API and Mobile Applications
1.1 Attack Vector: API Endpoint Vulnerabilities API endpoints serve as crucial communication channels between the frontend and backend systems. However, if not properly secured, they can become vulnerable to exploitation. Attackers may inject malicious code or execute unauthorized actions.
How Attack: Injection Attacks, Unauthorized Access Examples:
- SQL Injection: Attackers insert malicious SQL queries through user inputs, potentially leading to unauthorized data access or data loss.
- Authentication Bypass: Flaws in authentication mechanisms can allow attackers to bypass authentication and gain unauthorized access to sensitive resources.
Case Study: A breach occurs when an attacker injects malicious code through an unsanitized GraphQL input, gaining unauthorized access to user data or compromising the application's functionality.
Evidence: Notable incidents of API exploitation include the Equifax data breach, where attackers exploited a vulnerable API to gain access to personal information of millions of users.
1.2 Attack Vector: Mobile Application Vulnerabilities Mobile applications are a critical component of Netflix's user experience. However, vulnerabilities in these applications can lead to unauthorized access, data leakage, and compromise of the user's device.
How Attack: Reverse Engineering, Data Leakage Examples:
- Insecure Data Storage: Storing sensitive data, such as user credentials or tokens, in an insecure manner on the device, makes it accessible to attackers.
- Man-in-the-Middle Attacks: Attackers intercept communication between the mobile app and backend servers, enabling them to eavesdrop or manipulate data.
Case Study: A compromised mobile application allows attackers to extract personal user information or inject malicious code, leading to unauthorized access or data breaches.
Evidence: The Checkm8 vulnerability affecting iOS devices enabled attackers to perform full device compromise, potentially leading to unauthorized access to sensitive data.
- Backend: Spring Boot, Netflix Zuul, Netflix Eureka
2.1 Attack Vector: Misconfiguration and Authentication Weaknesses The backend services in Netflix's architecture, such as Spring Boot, Netflix Zuul, and Netflix Eureka, play a crucial role in processing and managing requests. However, misconfigurations and weak authentication mechanisms can create entry points for attackers.
How Attack: Server Misconfigurations, Weak Credentials Examples:
- Server Misconfigurations: Exposing unnecessary ports or services, outdated software, or default credentials can provide entry points for attackers.
- Weak Credentials: Using weak passwords or sharing credentials among multiple users can result in unauthorized access.
Case Study: A data breach occurs due to an unpatched vulnerability in one of the backend services, allowing attackers to gain unauthorized access to sensitive data.
Evidence: The Capital One breach involved attackers exploiting a misconfigured Web Application Firewall (WAF) to gain unauthorized access to customer data.
2.2 Attack Vector: Distributed Denial of Service (DDoS) A distributed denial of service (DDoS) attack aims to overwhelm backend services, rendering them unavailable to legitimate users.
How Attack: Overwhelming Backend Services Examples:
- Botnet Attacks: Attackers control a network of compromised devices (botnet) to launch massive DDoS attacks on the backend infrastructure.
- Resource Exhaustion: Exploiting vulnerabilities or inefficiencies in the application or network stack to exhaust system resources.
Case Study: A DDoS attack disrupts the availability of Netflix's services, causing inconvenience to users and potentially leading to financial losses.
Evidence: The Mirai botnet, which targeted IoT devices, caused widespread disruptions by launching massive DDoS attacks on various online services.
- Databases: EV Cache, Cassandra, CockroachDB, MySQL
3.1 Attack Vector: Database Exploitation Databases are repositories of valuable data, making them attractive targets for attackers. Exploiting vulnerabilities in databases can result in unauthorized access, data manipulation, or execution of malicious commands.
How Attack: SQL Injection, Privilege Escalation Examples:
- SQL Injection: Attackers insert malicious SQL queries through user inputs, potentially leading to unauthorized data access or data loss.
- Privilege Escalation: Exploiting database misconfigurations or vulnerabilities to elevate user privileges and gain unauthorized access to data.
Case Study: A successful SQL injection attack allows attackers to extract sensitive user information or modify the database's contents.
Evidence: The Ashley Madison data breach involved attackers using SQL injection to extract user data, leading to significant privacy breaches.
- Messaging/Streaming: Apache Flink, Kafka
4.1 Attack Vector: Message Queue and Streaming Vulnerabilities Messaging and streaming components, such as Apache Flink and Kafka, enable real-time data processing and communication. However, vulnerabilities in these systems can lead to tampering with messages, interception of sensitive data, or disruption of services.
How Attack: Message Tampering, Replay Attacks Examples:
- Message Tampering: Attackers modify messages in transit to manipulate application behavior or extract sensitive information.
- Replay Attacks: Attackers intercept and replay valid messages to bypass security controls or perform unauthorized actions.
Case Study: An attacker intercepts and modifies streaming messages, leading to the delivery of malicious content or unauthorized access to sensitive data.
Evidence: The Capital One breach involved a misconfigured WAF that allowed attackers to extract sensitive messages and gain unauthorized access.
- Video Streaming: Netflix Open Connect, Amazon CloudFront, Amazon S3
5.1 Attack Vector: Content Delivery and Storage Attacks Netflix's video streaming relies on robust content delivery and storage systems. However, vulnerabilities in these systems can result in unauthorized access to streaming content or manipulation of video content.
How Attack: Unauthorized Content Access, Man-in-the-Middle Examples:
- Unauthorized Content Access: Attackers exploit misconfigurations or vulnerabilities to gain unauthorized access to premium streaming content.
- Man-in-the-Middle: Attackers intercept and manipulate video streams, potentially injecting malicious content or conducting surveillance.
Case Study: Unauthorized individuals gain access to premium content by exploiting a misconfiguration in the content delivery infrastructure.
Evidence: The Sony Pictures Entertainment breach resulted in unauthorized access to unreleased movies, leading to significant financial and reputational damage.
- Big Data: Amazon S3, Amazon Redshift, Iceberg, Druid
6.1 Attack Vector: Big Data Infrastructure Vulnerabilities Big data infrastructure components, such as Amazon S3, Amazon Redshift, Iceberg, and Druid, handle vast amounts of sensitive data. Vulnerabilities in these systems can result in unauthorized access or manipulation of data analytics results.
How Attack: Data Exposure, Misconfigured Storage Examples:
- Data Exposure: Misconfigured access controls or insecure data storage practices can lead to unauthorized access or data leakage.
- Misconfigured Storage: Inadequate security configurations in data lakes or object storage systems can expose sensitive data to unauthorized individuals.
Case Study: A breach occurs when attackers exploit a misconfigured Amazon S3 bucket, leading to unauthorized access to sensitive data.
Evidence: The Verizon data breach involved misconfigured security settings on an Amazon S3 bucket, exposing millions of customer records.
- CI/CD: Jira, Atlassian, Netflix Atlas, Jenkins, Spinnaker
7.1 Attack Vector: Weaknesses in Continuous Integration and Deployment Continuous Integration and Deployment (CI/CD) systems streamline the software development and delivery process. However, vulnerabilities in these systems can result in unauthorized code deployment, injection of malicious code, or disruption of the software delivery pipeline.
How Attack: Unauthorized Code Deployment, Build System Exploits Examples:
- Unauthorized Code Deployment: Attackers gain unauthorized access to CI/CD systems and inject malicious code into the application's build process.
- Build System Exploits: Attackers exploit vulnerabilities in build systems to execute arbitrary commands or escalate privileges.
Case Study: Attackers compromise the CI/CD pipeline, leading to the compromise of the build process, injecting malicious code into the final application, or disrupting the software delivery pipeline.
Evidence: The Codecov breach involved attackers exploiting vulnerabilities in the CI/CD process, resulting in the compromise of thousands of customer credentials.
Conclusion:
The security vulnerabilities identified in the various components of the Netflix architecture highlight the critical importance of robust security measures. To ensure the protection of sensitive data and maintain user trust, Netflix should prioritize comprehensive security practices. This includes conducting regular security assessments, implementing secure coding practices, implementing strong authentication and authorization mechanisms, and continuously monitoring the infrastructure for potential vulnerabilities. By staying proactive and vigilant in addressing these potential vulnerabilities, Netflix can enhance the security posture of its architecture and safeguard both its infrastructure and user data.
Please note that the vulnerabilities mentioned in this blog post are hypothetical, and the actual security practices and safeguards implemented by Netflix may differ significantly.